¿Qué es GDPR?
En 2018 entró en vigor Reglamento General de Protección de Datos – GDPR en sus siglas en inglés. Esta normativa afecta a todas las empresas que operen con datos personales dentro del territorio de la Unión Europea.
En este sentido, el GDPR pretende reforzar los derechos de los sujetos de información. Es decir, facilitar a los consumidores un control efectivo sobre los datos personales que en cierto momento entregar a una empresa.
En este contexto, la violación de datos se tipifica como “violación de la seguridad que lleva a la destrucción, pérdida, alteración, revelación no autorizada de, o el acceso a, información personal transmitida, almacenada o procesada ya sea de forma accidental o ilegal”.
Aplicación
- Implica la PRIVACIDAD POR DISEÑO. Es decir, la privacidad como aspecto central en la configuración de los nuevos productos y/o procesos.
- También implica el empleo de un lenguaje claro y sencillo, conciso y transparente.
- Asimismo, se hace necesario incorporar CONTROLADORES. Responsables internos encargados de demostrar el cumplimiento del GDPR.
- PIA, evaluación del impacto de la seguridad. Es decir, identificar y minimizar riesgos de incumplimiento como requisito formal.
- Además, se incorporan nuevos derechos al sujeto de información. Por ejemplo, AL OLVIDO, PORTABILIDAD DE DATOS o A OBJETAR (que los datos no se puedan utilizar en el marketing directo).
Sanciones por incumplimiento
- En primer lugar, las empresas deberán comunicar las fisuras en sus medidas de seguridad de la información en un plazo de 72 horas.
- Además, multas de hasta 20 millones de euros o del 4% del volumen de negocio total (se optará por la de mayor cuantía).
- También deberán hacerse cargo de las posibles indemnizaciones económicas por los daños causados.
- Asimismo, las empresas que incumplan la normativa deberán hacer pública su infracción. Con el consiguiente daño reputacional que supone.
- Por otro lado, cada Estado podrá asociar las sanciones administrativas con posibles sanciones legales.
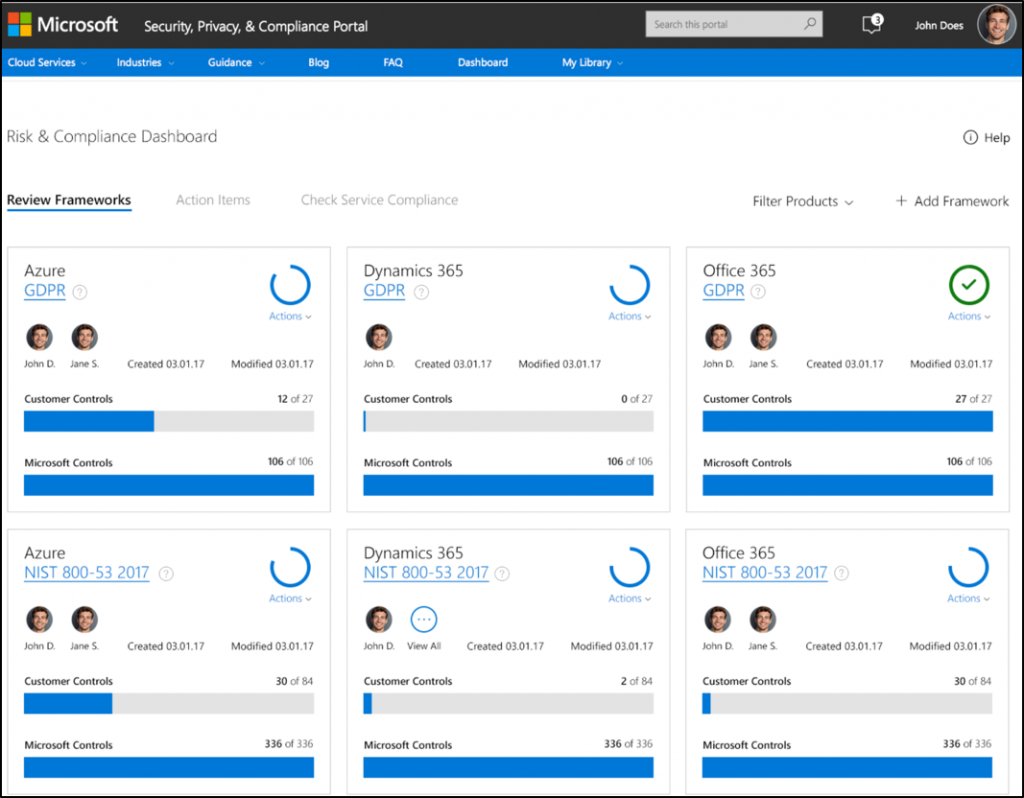
Microsoft Azure | GDPR
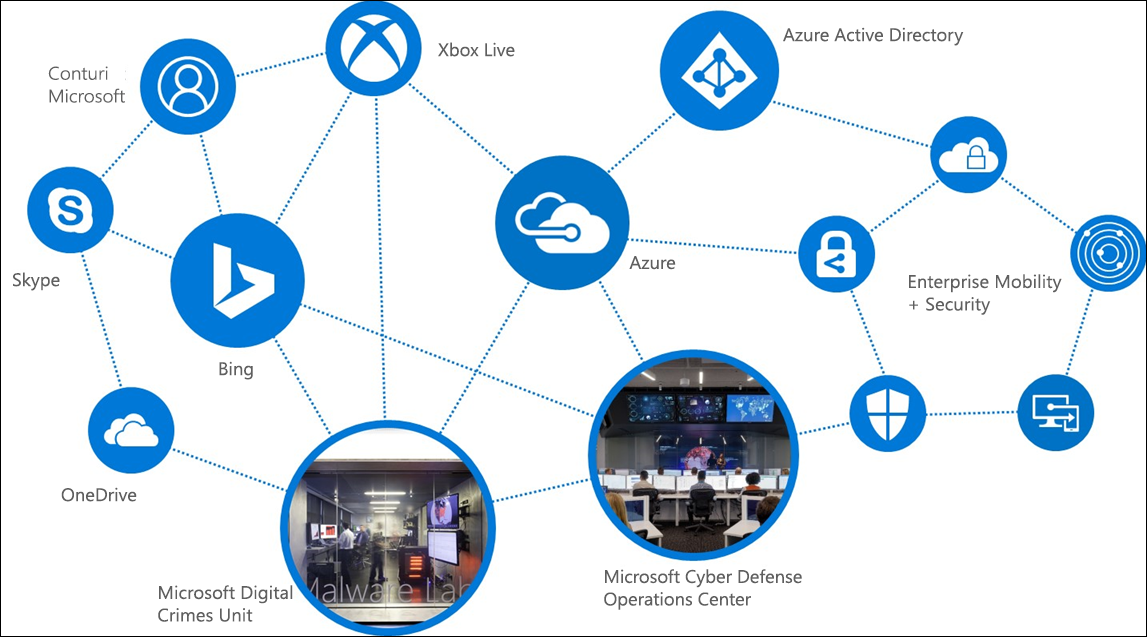
Uno de los requisitos del GDPR es la capacidad de identificar los datos y controlar quién tiene acceso a ellos. En este sentido, Microsoft Azure permite la administración de identidades y credenciales de los usuarios y el control de acceso mediante:
- AZURE ACTIVE DIRECTORY (Azure AD). A través de esta herramienta, sólo determinados usuarios autorizados pueden acceder a los datos, entornos informáticos y aplicaciones.
- AZURE INFORMATION PROTECTION. Garantiza que los datos sean identificables y cumplan los requisitos de seguridad.
Asimismo, GDPR requiere la protección de los datos contenidos en los sistemas, la generación de informes y el control del cumplimiento normativo.
Por ejemplo, ofrece visibilidad y controles en relación con la seguridad de la nube. Para ello, supervisa recursos, ofrece recomendaciones de seguridad y ayuda en la detección e impedimento de amenazas.
Tanto los datos en reposo como en tránsito están protegidos. Es decir, protección de datos mientras se transfieren de una aplicación al entorno de Azure.
Se encarga de proteger claves criptográficas, certificados y contraseñas. Además, incluye la garantía de que Microsoft no puede ver ni extraer las claves. Por su parte, los registros de Azure permiten supervisar y auditar el uso de claves almacenadas.
Es decir, opciones configurables de auditoría y registros de seguridad. Además, Log Analytics es capaz de recopilar y analizar datos generados por recursos locales o en la nube.
Localiza filtraciones y es capaz de identificar a los atacantes. Lo logra a través de tecnologías de análisis de comportamiento y detección de anomalías.
Office 365 | GDPR
Para garantizar la identificación y la administración en el acceso a los datos personales, Office 365 dispone de:
- PREVENCIÓN DE PÉRDIDA DE DATOS (DLP). Por ejemplo, capaz de identificar más de 80 tipos de datos confidenciales comunes.
- GOBIERNO DE DATOS AVANZADO. Útil a la hora de encontrar, clasificar y definir directivas. También para adoptar medidas para administrar el ciclo de vida de los datos.
- OFFICE 365 eDISCOVERY. Una función muy importante ya que es capaz de encontrar texto y metadatos en todos los recursos de Office 365. Es decir, SHAREPOINT ONLINE, ONEDRIVE PARA LA EMPRESA, SKYPE PARA LA EMPRESA y EXCHANGE ONLINE.
- CUSTOMER LOCKBOX. Para la autorización expresa de acceso a los datos personales.
En cuanto a la protección de los datos personales frente a amenazas de seguridad:
Por ejemplo, para proteger el correo electrónico.
Capaz de detectar amenazas avanzadas y ofrecer una protección proactiva.
Identifica usos anormales y de alto riesgo.
Encargado de supervisar y hacer un seguimiento de las actividades de los administradores y usuarios.
Microsoft Dynamics 365 | GDPR
Por su parte, Microsoft Dynamics 365 permite administrar y supervisar el acceso a los datos de las siguientes maneras:
- ROLES. Es decir, limitando las tareas que un usuario determinado puede realizar.
- REGISTROS. Del mismo modo, es capaz de limitar el acceso a ciertos registros.
- CAMPO. Y restringe el acceso a ciertos campos. Por ejemplo, podría ser el acceso a la información personal.
- AZURE ACTIVE DIRECTORY (Azure AD). Por último, dispone de esta herramienta de la nube que permite controlar los accesos de los usuarios.
Respecto a la protección de los datos personales, Microsoft Dynamics 365 se vale de:
Importante al integrar requisitos de seguridad en cada paso del proceso.
Tanto en tránsito entre dispositivos de usuarios y centros de datos, como en reposo en las bases de datos.
MICROSOFT ENTERPRISE MOBILITY +SECURITY | GPDR
Ya en su diseño, Microsoft incorporó funciones de seguridad líderes en la industria. Por lo tanto, la transición al nuevo marco legal europeo no resulta tan complicada como podría ser.
En este sentido, cuenta con capacidades que le permiten asegurar la integridad de los datos personales.
Asimismo, permite administrar qué datos se mantienen, dónde residen y puede controlar el uso que los usuarios hacen de los mismos y su forma de acceso. Del mismo modo, es capaz de establecer controles de seguridad efectivos para impedir y detectar vulnerabilidades e incidencias.
- AZURE ACTIVE DIRECTORY (Azure AD). Se asegura de que únicamente los usuarios autorizados tengan acceso a entornos informáticos, datos y aplicaciones.
- MICROSOFT CLOUD APP SECURITY. Para descubrir todas las apps de la nube en su entorno. También permite identificar a los usuarios y el uso y recibir un puntaje de riesgo para cada app.
- MICROSOFT INTUNE. Ofrece protección a los datos alojados en equipos personales y dispositivos móviles. Por lo tanto, es una herramienta muy importante.
- MICROSOFT ADVANCED THREAT ANALYTICS. Localiza filtraciones y es capaz de identificar a los atacantes. Para ello, utiliza tecnologías de análisis del comportamiento y de detección de anomalías.
MICROSOFT SQL SERVER y AZURE SQL DATABASE | GDPR
En virtud al control en el acceso a la base de datos y la administración del uso de los mismos, existen garantías que permiten las autorizaciones en diferentes niveles:
- FIREWALL DE AZURE SQL DATABASE. Capaz de limitar el acceso restringiendo ciertas bases específicas del servidor. Además, permite exclusivamente conexiones autorizadas.
- AUTENTICACIÓN DE SQL SERVER. Para que sólo los usuarios autorizados pueden acceder a las bases de datos del servidor. Admite tanto la autenticación de Windows como inicios de sesión de SQL Server.
- AUTORIZACIÓN DE SQL SERVER. Dado que la seguridad en SQL Server y Database está basada en roles, permite mantener un control de datos a través de la pertenencia a roles y los permisos de nivel de objeto.
- ENMASCARAMIENTO DINÁMICO DE DATOS (DDM). A través del enmascaramiento de datos a usuarios o aplicaciones, se controla el acceso a la información.
- SEGURIDAD DE NIVEL DE FILA (RSL). También para implantar restricciones a las filas de datos.
Para la protección de los datos frente a las amenazas de seguridad, SQL Server y SQL Database disponen de:
- CIFRADO DE DATOS TRANSPARENTE. Cifrando la base de datos, protege de forma efectiva los daros en reposo. Además, ofrece copas de seguridad relacionadas y archivos de registro de transacciones.
- PROTOCOLO DE SEGURIDAD DE LA CAPA DE TRANSPORTE (TLS). Por su parte, TLS se encarga de la protección de los datos en tránsito en las conexiones de SQL Database.
- ALWAYS ENCRYPTED. Un elemento muy innovador, diseñado para proteger los datos confidenciales en SQL. Cifra los datos sin revelar las claves ni siquiera al motor de la base de datos.
- AUDITORÍA DE SQL DATABASE y AUDITORÍA DE SQL SERVER. Para realizar un seguimiento de los eventos que han ocurrido en la base de datos y registrarlos como auditoría.
- SQL DATABASE THREAT DETECTION. A través de un conjunto avanzado de algoritmos, se encarga de detectar actividades anómalas que podrían ser amenazas.
WINDOWS 10 y WINDOWS SERVER 2016 | GDPR
La seguridad ha sido una prioridad en el diseño de Windows 10 y Windows Server 2016. En este sentido, cumplen con los requisitos que marca el nuevo reglamente GDPR a través de:
- WINDOWS HELLO. Una alternativa a las contraseñas de nivel empresarial que utiliza un método natural (biométrico) o conocido (PIN).
- WINDOWS DEFENDER. Se trata de una solución antimalware capaz de detectar cualquier malware y protegerse del mismo.
- PROTECCIÓN CONTRA AMENZAS AVANZADA (ATP) DE WINDOWS DEFENDER. Seguridad avanzada a través de la detección, investigación y respuesta ante incidentes.
- DEVICE GUARD. Permite bloquear servidores y dispositivos como protección ante amenazas avanzadas. Así, los dispositivos sólo podrían ejecutar las aplicaciones autorizadas.
- CREDENTIAL GUARD. A través de esta funcionalidad es posible aislar los secretos de los dispositivos e impedir el acceso a ellos. Por ejemplo, tokens o inicios de sesión.
- CIFRADO DE UNIDAD BITLOCKER. Para proteger los datos cuando un dispositivo se pierde o es robado.
- WINDOWS INFORMATION PROTECTION. En este caso, se trata de la protección de los datos frente a usuarios no autorizados y aplicaciones. Asimismo, ayuda a impedir filtraciones de documentos sensibles para la empresa.
- MÁQUINAS VIRTUALES BLINDADAS. A través de BitLocker, se cifran discos y máquinas virtuales.
- JUST ENOUGH ADMINISTRATION AND JUST IN TIME ADMINISTRATION. Para limitar las competencias y el tiempo de actuación de los administradores.
¿Quieres una cita con un consultor?
Contacta con nosotros sin compromiso y te asesoramos. ¡Arranca la transformación digital de tu empresa!